![]() BitLocker is a volume encryption feature of Windows. Paired with the Microsoft BitLocker Administration and Monitoring (MBAM) software, this feature meets the requirement of the UVM Information Security policy for encryption of all laptops.
BitLocker is a volume encryption feature of Windows. Paired with the Microsoft BitLocker Administration and Monitoring (MBAM) software, this feature meets the requirement of the UVM Information Security policy for encryption of all laptops.
Prerequisites
To use UVM’s BitLocker services, the following requirements must be met:
- The computer must be joined to the Campus Active Directory domain or UVM’s Microsoft Entra ID tenant.
- The operating system must be Enterprise editions of Windows 10 or Windows 11.
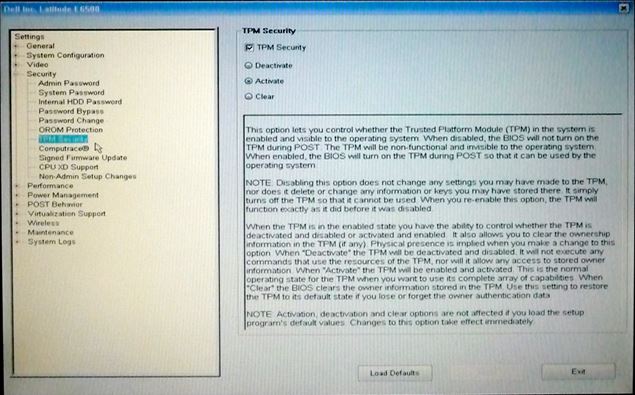
- The Trusted Platform Module (TPM) must be enabled.
If the computer was set up by the Tech Team, a support hub, or the UVM Bookstore, and the above requirements were met at that time, BitLocker Drive Encryption should be enabled by default. If not, it can be turned on manually using the steps below.
Enable/Activate TPM
Install the MBAM client
We are using the Microsoft BitLocker Administration and Monitoring software to provide additional capabilities for our clients and support staff. Machines imaged with LiteTouch will install the MBAM client automatically.
- Log in to the machine using UVM credentials. Local account credentials will not work.
- The MBAM client is available at the following UNC path: \\files.uvm.edu\shared\software\management\BitLocker\MBAMClient
- Install the 32-bit or 64-bit version as appropriate. When the installer completes, reboot the machine.
- Make sure the machine has an active network connection. Within 90 minutes of reboot, you should be prompted to encrypt your drive.
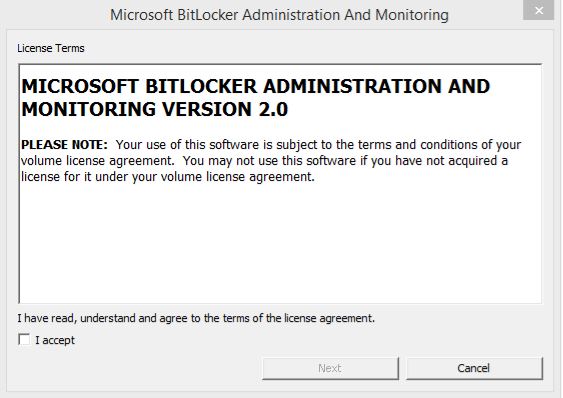
- Accept the licensing terms.
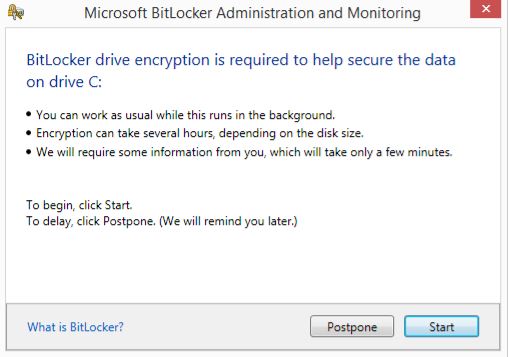
- “Start” the encryption process.
- The drive will begin encrypting and display the progress. This window may be closed without disrupting the encrypting process.
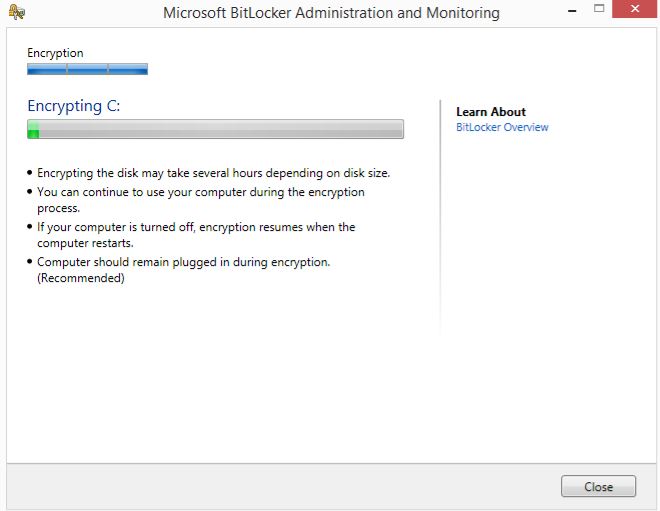
- Once encryption has begun, you can put your computer to sleep, shut it down, or restart it; the encryption process will resume when you restart or wake the device. When encryption has finished, the icon for the encrypted volume will change in Windows Explorer:

Patch the MBAM Client
Starting with Windows 10 version 1909 and later, a MBAM client patch may be required for it to work correctly. If you are consistently getting a message stating that your drive failed to encrypt, follow the instructions below.

- Login to the machine using DOMAIN credentials. Local account credentials will not work.
- The MBAM patch is available at the following UNC path: \\files.uvm.edu\shared\software\management\BitLocker\May 2019 Servicing Release
- Install the 32-bit or 64-bit version as appropriate. When the installer completes, reboot the machine.
BIOS updates on BitLocker Encrypted drives
It is recommended that you backup data before attempting BIOS updates. Please ensure data has been backed up before proceeding.
- Login to the machine as an Administrator. (Use a *.tech account or other local Administrator)
- Open a PowerShell window as Administrator.
- Disable BitLocker protectors with the following command:
manage-bde -protectors c: -disable
- Install the BIOS update.
- When the BIOS update completes, log in to the machine as an administrator and run the following command to re-enable the BitLocker protectors:
manage-bde -protectors c: -enable
- You can confirm that the protectors have been re-enabled by running:
manage-bde –protectors c: -get